User Activity Documentation Linked to Keevee1999 and Alerts Logs
User activity documentation plays a vital role in organizations like Keevee1999. It provides a framework for compliance and supports informed decision-making through insights into user interactions. Analyzing alerts logs reveals important information about system anomalies and alert frequency. This analysis not only enhances threat detection but also encourages a proactive security stance. Understanding these elements raises questions about potential vulnerabilities and the overall effectiveness of current security measures.
Understanding User Activity Documentation
While many organizations recognize the importance of tracking user activity, understanding the nuances of user activity documentation is essential for maximizing its effectiveness.
Accurate documentation of user behavior not only ensures compliance but also enhances decision-making processes. By focusing on documentation accuracy, organizations can glean insights into patterns and trends, ultimately fostering an environment that values user independence and informed action.
Analyzing Alerts Logs
When organizations analyze alerts logs, they uncover critical data that reveals user interactions and system anomalies.
This process involves assessing alert frequency to identify unusual patterns indicative of potential issues. Effective anomaly detection allows organizations to respond proactively, ensuring system integrity and user security.
Identifying Patterns and Potential Threats
Identifying patterns and potential threats requires a meticulous examination of user activity data, as this analysis can reveal underlying vulnerabilities within an organization’s systems.
By scrutinizing user behavior, analysts can enhance threat detection capabilities, enabling proactive measures against possible breaches.
Recognizing unusual patterns in activity serves as a cornerstone for safeguarding information, ultimately empowering organizations to maintain security while fostering a culture of freedom and trust.
Enhancing Security and System Functionality
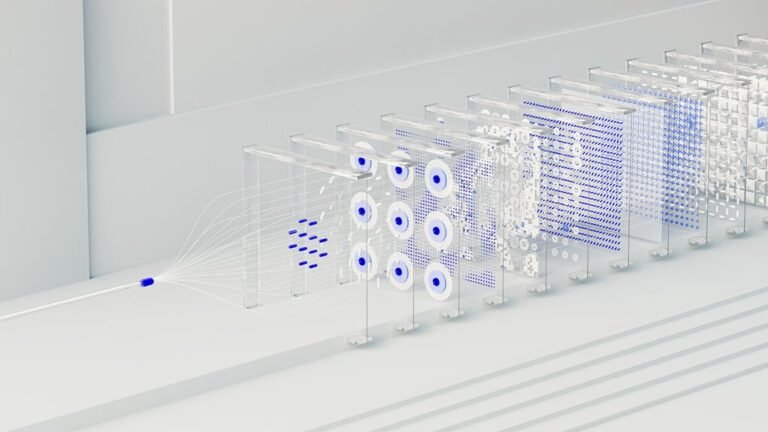
To enhance security and system functionality, organizations must implement a multi-layered approach that integrates advanced technologies and best practices.
Critical components include robust user authentication measures and stringent access control protocols.
Conclusion
In conclusion, user activity documentation serves as a foundation for compliance, analysis, and decision-making within Keevee1999. By systematically analyzing alerts logs, organizations can identify patterns, detect anomalies, and assess potential threats. This proactive approach not only enhances security measures but also optimizes system functionality. Ultimately, the integration of thorough documentation and meticulous analysis fosters a safer environment, promotes informed decision-making, and strengthens the overall integrity of the organization’s operational framework.